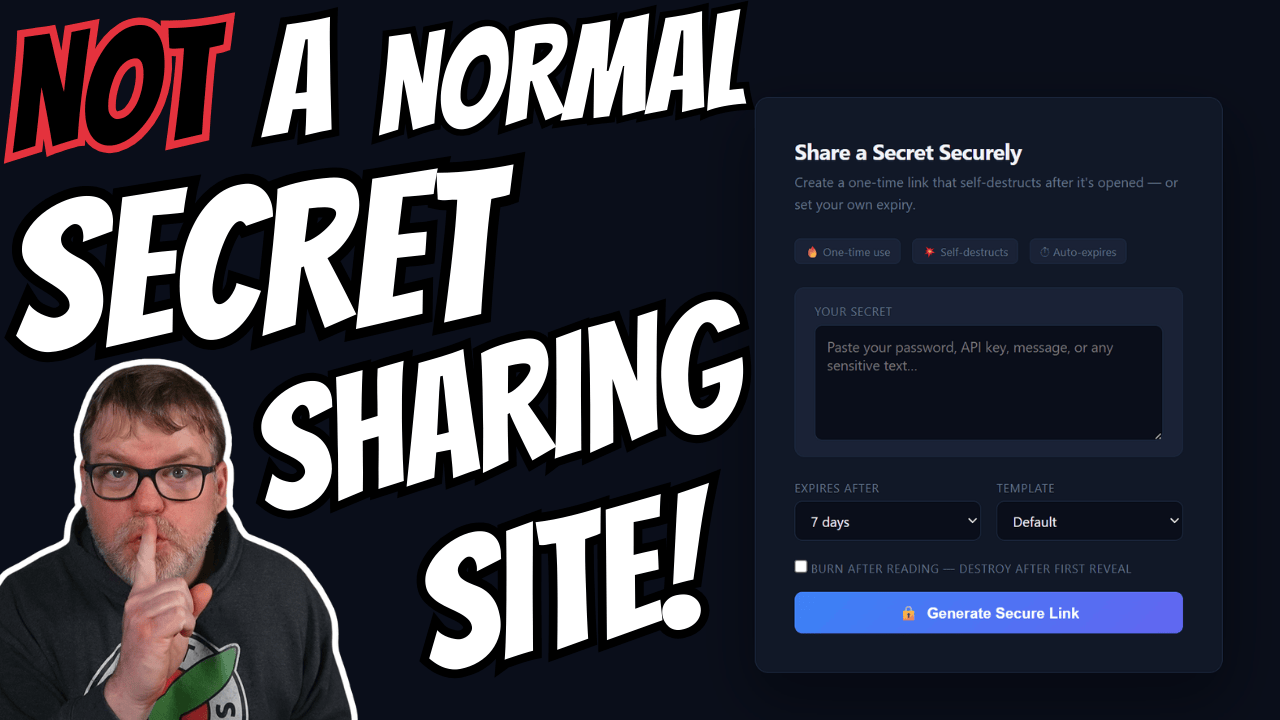
Have you ever wanted to flip the script on a scammer?
Instead of ignoring the message or blocking the number, what if you could send them a link that looks like a secure password-sharing page — but quietly logs information about the person who clicks it?
That’s the concept behind Null Vault.
Built as an experimental project through AI-assisted development, Null Vault is a self-hosted web application that mimics a legitimate secret-sharing platform while functioning as a lightweight intelligence-gathering honeypot.
What Is Null Vault?
Null Vault is an open-source, self-hosted web application designed to appear as a secure “burn-after-reading” secret-sharing service.
However, it is not intended to protect secrets.
Its primary function is deception. The goal is to entice malicious actors — particularly scammers — into clicking a link they believe contains sensitive data. When they do, the application captures telemetry and behavioral data for analysis.
This makes Null Vault less of a password tool and more of a controlled social engineering platform.
How the Deception Works
The workflow is straightforward:
- A scammer requests sensitive information.
- You respond by saying you’ll share it securely via a password-sharing link.
- You generate a public URL inside Null Vault.
- The scammer clicks the link and attempts to retrieve the “secret.”
- You monitor the activity from a private control panel.
From the visitor’s perspective, they see a convincing secret-sharing interface and can even click “Reveal Secret.”
From your perspective, each interaction generates logs and metadata.
Customizable Landing Themes
To increase believability, Null Vault supports multiple visual templates that mimic common online services, including:
- Generic secret-sharing pages
- Banking portal-style layouts
- Crypto wallet interfaces
- Corporate document sharing portals
- Invoice or payment-themed pages
Each template alters the look and feel of the landing page. The goal is to match the scenario and make the interaction appear natural to the target.
The Control Panel: What You Can Monitor
Once someone visits the public link, the private control URL begins collecting data. The dashboard includes several key sections.
Overview
- Total views
- Reveal events
- Failed access attempts
- Burned link activity
- Active/inactive link status
This provides an immediate snapshot of how the link has been interacted with.
Timeline
The timeline logs each visit with:
- Timestamp
- IP address (partially obfuscated by default)
- Referrer data
- Indicators of rapid refresh or repeat visits
This helps identify persistent or automated behavior.
Device and Environment Details
Null Vault captures client-side metadata such as:
- Device type (desktop, mobile, etc.)
- Operating system indicators
- Browser user agent strings
- Client hints
While not foolproof, this can provide useful context about the environment being used.
IP Intelligence Pivots
The dashboard includes shortcuts to external reputation services like:
- AbuseIPDB
- GreyNoise
These links allow quick lookups without integrating third-party APIs directly into the application.
Webhooks and Alerts
Users can configure webhooks to trigger notifications (for example, to a Discord channel) whenever a secret is revealed.
This enables real-time monitoring rather than manual dashboard refreshing.
Raw Logs
For deeper inspection, structured raw logs are available, providing all captured data in a less polished but more detailed format.
Burn-After-Reading and Expiration Controls
To maintain the illusion of legitimacy, Null Vault supports:
- Configurable expiration durations
- Burn-after-read functionality
- Manual link termination
When a link is burned, future access attempts are logged as failures. This can provide insight into whether the target continues attempting to retrieve the content.
AI-Assisted Development and “Vibe Coding”
A defining aspect of Null Vault is how it was built.
The project was developed primarily through AI-assisted coding rather than traditional programming experience. It evolved through iterative prompting, debugging, testing, and refinement.
This approach allowed rapid feature development but also introduced occasional bugs and inconsistencies. The project openly acknowledges its AI-assisted origins and positions itself as an experiment rather than a polished enterprise product.
It raises an interesting question for the security community:
Does the method of creation matter if the code is transparent and open source?
Not a Secure Vault — A Deception Platform
It is important to be clear:
Null Vault does not use hardened encryption.
It is not intended to securely store sensitive data.
It should not be used for legitimate secret protection.
Its purpose is deception and telemetry collection.
That places it somewhere between:
- A social engineering lab tool
- A lightweight honeypot
- An OSINT experiment
- A scammer engagement platform
Used responsibly, it can serve as an educational exercise in understanding attacker behavior.
Deployment Overview
Null Vault is designed to be self-hosted using containerized infrastructure such as:
- Docker
- Portainer
- Nginx Proxy Manager
The full setup process — including environment configuration, reverse proxy setup, DNS configuration, and SSL certificate issuance — is demonstrated step-by-step in the accompanying SYNACK Time video.
Rather than duplicating installation instructions here, the video walkthrough provides the complete deployment guide.
Ethical and Legal Considerations
Tools that intentionally deceive—even malicious actors—exist in a legal and ethical gray area depending on jurisdiction.
Before deploying something like Null Vault, consider:
- Local laws regarding data collection
- Privacy regulations
- Logging requirements
- Whether engagement may escalate the situation
For many people, reporting and blocking scammers remains the safest course of action.
Null Vault is best viewed as an educational or experimental project rather than a mainstream defensive tool.
Final Thoughts
Null Vault represents:
- Creative defensive experimentation
- Practical lessons in social engineering
- A demonstration of AI-assisted development
- An open-source exploration of deception tooling
It is not production-grade security software.
It is not a secure password manager.
But it is an intriguing experiment in flipping the script on social engineers — and a conversation starter about how AI is changing software development.
If you’d like to see it demonstrated live and deployed in a real environment, check out the corresponding SYNACK Time video and decide for yourself:
Is this something you’d use — or something you’d rather avoid?